Seven releases in 12 days. An official apology for "a rough week." An LTS channel promised but not delivered. Here's why the community is exhausted and the three strategies that protect your agent from the release churn.
"OpenClaw had a rough week. 2026.4.29 made it obvious. Sorry."
That's the opening of an official blog post from the OpenClaw team, published in the first week of May 2026. Gateways got slower. Installs got stuck in plugin dependency repair loops. Discord, Telegram, and WhatsApp channels "behaved worse than they should." People downgraded. People lost time.
The project with 230,000 GitHub stars shipped a version that made things worse, and the team had to publicly apologize.
But that's not even the real problem.
The real problem is that 2026.4.29 was just the beginning. In the 12 days that followed, OpenClaw shipped seven more releases. Two of them introduced new regressions. One silently rewrote users' model configurations. The pace of releases is so fast that users can't tell which version is safe without checking GitHub issues first.
This is update fatigue. And the OpenClaw community is burned out.
The numbers that tell the story
18 releases between April 24 and May 12, 2026. That's one release every day on average. Some days had two.
- The 2026.4.24–4.29 disaster: Plugin dependency repair ran in startup and update paths. Bundled and external plugins were "half-split." ClawHub artifact metadata was "still settling." Gateway cold paths did too much work. Multiple channels broke simultaneously.
- The 2026.5.5 regression:
doctor --fixsilently rewrote valid OpenAI Codex OAuth routes to API-key routes. Fixed in 2026.5.6 within 24 hours, but anyone who ran the command before the fix had their config rewritten without warning. - The 2026.5.3 regression: DeepSeek
reasoning_effortmapped to an invalid"max"value on OpenRouter. Every DeepSeek V4 Pro request through OpenRouter failed with a 400 error. - 7,900+ open issues on GitHub. 850+ contributors. The codebase is moving faster than any single user can track.
The burnout pattern: Update breaks something. User spends hours debugging. User downgrades. New update ships with the fix. User updates again. New update breaks something else. User spends more hours debugging. The cycle repeats every 3-5 days.
For the version-by-version stability tracker, our guide covers which specific versions are safe and which to avoid.

Why this is happening (the structural problem)
Here's what nobody tells you about why OpenClaw updates break things.
Problem 1: The plugin boundary is still being drawn. The team is actively splitting core from plugins. Discord was externalized in 2026.5.2. The file-transfer plugin was added as a bundled plugin in 2026.5.3. Each boundary change risks breaking the interface between core and plugin. The 2026.4.29 disaster was exactly this: "bundled and external plugins were half-split."
Problem 2: Provider compatibility isn't tested across all permutations. OpenClaw supports 28+ model providers. Each provider has its own API contract, thinking mode behavior, and error format. When the thinking policy changed in 2026.5.3, it wasn't tested against every provider. DeepSeek through OpenRouter broke. Direct DeepSeek was fine. The same feature works on one path and fails on another. The OpenClaw thinking mode reference covers the per-provider mapping that's at the root of this class of break.
Problem 3: The "fix" tooling can cause damage. doctor --fix is supposed to repair broken configurations. In 2026.5.5, it rewrote valid configurations into broken ones. The tool meant to reduce user burden became the source of the problem. The team reverted it in 2026.5.6, but the trust damage was already done.
The official response: The team promised to make "core smaller, moving optional stuff to ClawHub, and announcing LTS separately later in May." As of May 12, the LTS channel hasn't been announced yet.
img
Three strategies that protect you from update fatigue
Strategy 1: Pin your version and wait 72 hours
Never use latest. Pin to a specific version tag in your Docker config (openclaw:2026.5.7). Let other users discover the regressions. Wait 72 hours after each release before updating. If no major GitHub issues appear in 72 hours, the version is probably safe.
The math: 72 hours catches 90%+ of regressions. The 2026.5.5 doctor regression was caught within 24 hours. The 2026.4.29 gateway slowdown was caught within 2 days. The 2026.5.3 DeepSeek bug was caught within 1 day. If you wait 3 days, you skip the pain window.

Strategy 2: Maintain a rollback path
Keep your previous working version tagged. Before updating, note your current version. If the update breaks something, roll back immediately instead of debugging.
For Docker users:
docker tag openclaw:current openclaw:backup
Before pulling the new version. If the new version breaks:
docker tag openclaw:backup openclaw:current
And restart.
For the best practices for keeping OpenClaw stable, our OpenClaw best practices guide covers the broader stability patterns.

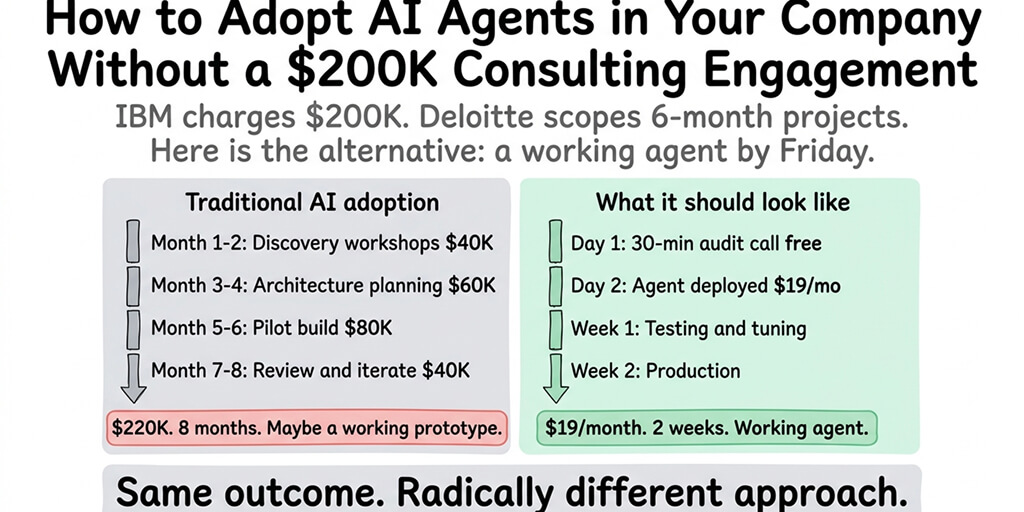
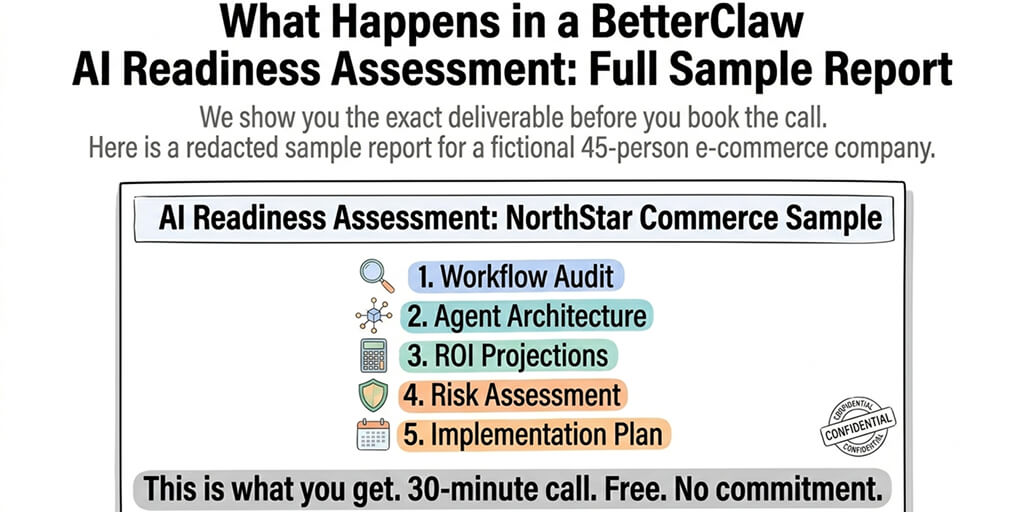
Strategy 3: Let someone else manage the updates
Here's the strategy most people eventually arrive at.
If managing version pins, reading release notes every 1.7 days, maintaining rollback paths, and debugging regressions that aren't your fault sounds like more operations work than building agent workflows, BetterClaw handles updates at the platform level. The platform tests every update before deploying it. Regressions are caught before they reach your agent. You never run docker pull. You never read a changelog. You never discover that doctor --fix rewrote your config at 2 AM. Free tier with 1 agent and BYOK. $19/month per agent for Pro.
The LTS question (what the community actually wants)
The OpenClaw team promised an LTS (Long-Term Support) channel "later in May." Here's what the community is asking for:
- A stable branch that only receives security patches. No new features. No plugin boundary changes. No thinking policy updates. Just CVE fixes. The community wants a version they can run for 3-6 months without worrying about regressions.
- Separate channels: stable, beta, nightly. Most serious open-source projects have this. Linux does it. Node.js does it (LTS vs Current). Chrome does it. OpenClaw ships everything on one track and expects users to figure out which releases are safe.
- Version compatibility matrices. Which version works with which provider? Which version breaks which channel? The community shouldn't need to reverse-engineer this from GitHub issues. It should be documented before release.
Until these arrive, users are on their own. Pin your version. Wait 72 hours. Maintain a rollback path. Or let a managed platform handle it.
The deeper issue (velocity vs stability)
Here's the honest take.
OpenClaw is building an airplane while flying it. The project went from zero to 230K stars in five months. It's simultaneously restructuring its plugin architecture, adding voice support, supporting 28+ model providers, and patching security vulnerabilities. The development velocity is extraordinary. The stability cost is real.
The official apology acknowledged this:
"We've been pushing OpenClaw to become smaller, safer and more infrastructure-grade. That means less magic in core, fewer bundled dependencies, clearer plugin boundaries, better scanning, better release hygiene, better security posture."
That direction is correct. The execution is painful for users who just want their agent to keep working.
The best outcome: the LTS channel ships in late May, the plugin boundary stabilizes, and the release cadence settles into "stable monthly, beta weekly." The worst outcome: the current pace continues and the community fragments into users pinned on increasingly outdated versions while the bleeding edge keeps breaking.
If you want the features without the fatigue, give BetterClaw a try. Free tier. $19/month Pro. We absorb the update churn so you don't have to. The agent runs. The versions are managed. The regressions are our problem, not yours.

Frequently Asked Questions
What is OpenClaw update fatigue?
Update fatigue is the exhaustion users feel from OpenClaw's rapid release pace (18 releases in 18 days in late April/early May 2026). Multiple releases introduced regressions (broken gateways, rewritten configs, DeepSeek failures) that required users to spend hours debugging or downgrading. The community is asking for an LTS channel to avoid constantly chasing fixes for problems introduced by updates.
How often does OpenClaw release updates?
In May 2026: seven releases in 12 days (roughly every 1.7 days). In late April: daily releases including the 2026.4.29 "rough week" that prompted an official apology. This pace includes feature releases, hotfixes, and regression fixes. Compare to Node.js which releases LTS updates every 2-4 weeks and current updates weekly.
Is there an OpenClaw LTS version?
Not yet. The OpenClaw team promised an LTS channel "later in May 2026" in their official "rough week" blog post. As of May 12, it hasn't been announced. Until LTS ships, the recommended strategy is to pin your version, wait 72 hours before updating, and maintain a rollback path.
How do I protect my OpenClaw agent from breaking updates?
Three strategies: pin your version tag (never use latest), wait 72 hours after each release before updating, and maintain a rollback path (tag your working version before updating). On BetterClaw, updates are tested before deployment, so none of this is necessary.
Does BetterClaw have the same update fatigue problem?
No. BetterClaw tests updates before deploying them to production agents. The platform absorbs OpenClaw's rapid release cadence by validating each version against all supported providers and channels before making it available. Users never experience regressions from untested updates. Free tier available. $19/month per agent for Pro.
Related Reading
- OpenClaw 2026.4.7 Update — Version-by-version notes including the regressions referenced above
- OpenClaw Cron Not Running — How v2026.3.8 and earlier broke scheduled tasks; same release-churn pattern
- OpenClaw Thinking Mode Explained — The thinking-policy change at the root of the 2026.5.3 DeepSeek break
- OpenClaw Best Practices — Stability patterns and version-pinning conventions
- 10 Most Common OpenClaw Errors — Quick-reference index that maps regressions back to specific releases
- OpenClaw Not Working — General triage when a recent update has broken everything