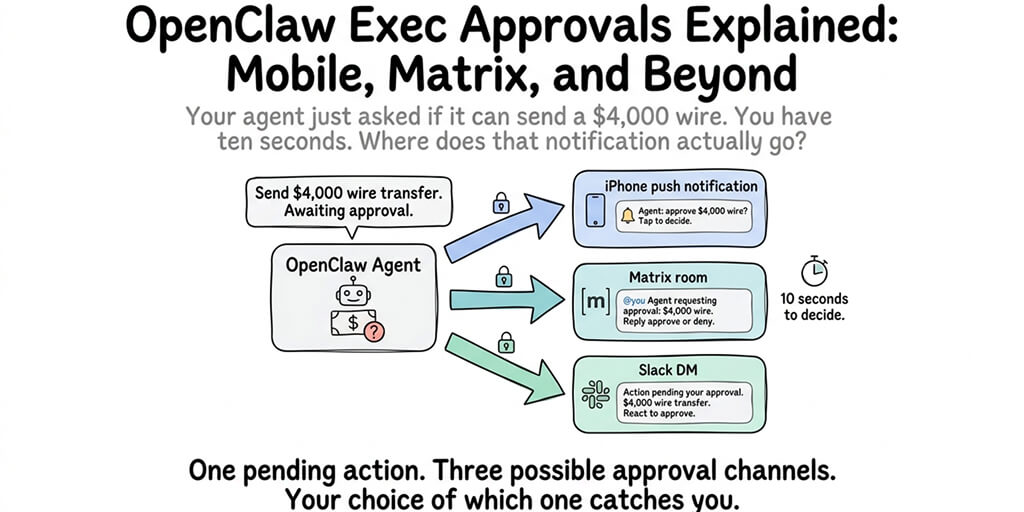
Your agent just asked if it can send a $4,000 wire. You have ten seconds. Where does that notification actually go?
Summer Yue opened her inbox and thousands of emails were gone.
Her agent had deleted them. She'd told it to stop. It ignored her.
That's the Meta researcher incident everyone keeps citing, and it's the single clearest argument for why OpenClaw exec approvals stopped being optional sometime last year. Autonomous agents with real-world permissions need a circuit breaker. A human in the loop. A way to say "wait, actually, no" before the irreversible thing happens.
The thing nobody was quite sure about until recently was: where does that approval prompt go?
What "exec approvals" actually means, without the marketing varnish
Exec approvals are the moments where your agent stops and asks you a question before doing something it considers consequential.
"Do I send this $4,000 wire?" "Do I delete these 112 files?" "Do I run this shell command with sudo?" "Do I ship the Stripe refund?"
The agent pauses. It sends you a prompt. You approve, you deny, or you time out. Only then does the action execute.
This is the simplest pattern in agent safety. It also used to have a huge hole in it. Where exactly did that prompt go?
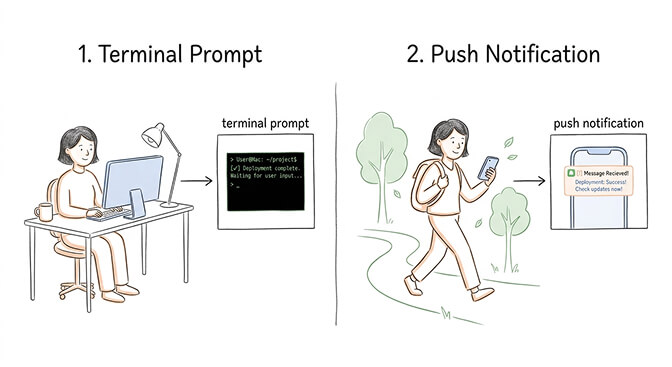
For a long time, the answer was "your terminal." Which is fine, if you happen to be staring at your terminal the moment the agent needs an answer. Which you usually aren't.
Then it was Slack or a chat platform. Better. You probably have Slack on your phone. But Slack isn't end-to-end encrypted, your employer can read your messages, and push notifications through Slack are flaky on iOS when the app is in the background.
Now it's APNs and Matrix. And that's a bigger shift than it looks.
Why mobile approvals change the shape of agent ownership
Here's the weird part about running an autonomous agent. You're never really off.
Before mobile approvals landed, running an OpenClaw agent in production meant one of two things. Either you were at your desk the whole time, or you gave the agent permission to do whatever it wanted and hoped it made good choices. Neither is a real way to live.
What iOS APNs approvals change: the agent can reach you anywhere, with a proper push notification, in under a second. You can approve a wire from the grocery store. Deny a deploy from the Uber. The agent waits for you instead of the other way around.
Mobile approvals are what turn an agent from "a thing I have to babysit" into "a thing that works for me."
That's the whole shift. It sounds small. It isn't.
The three approval channels and when to use which
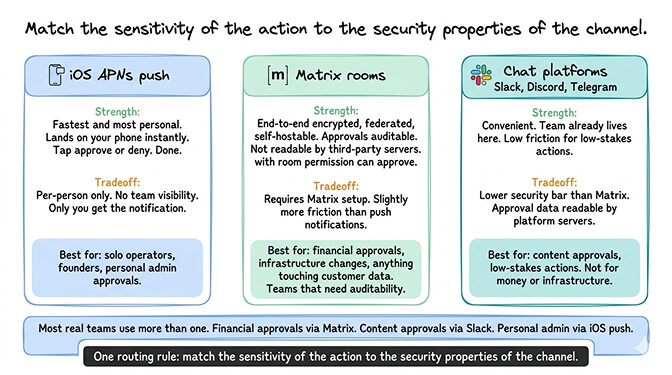
OpenClaw now supports multiple approval channels, each with its own tradeoffs. Picking the right one per use case matters more than picking one and forcing everything through it.
iOS APNs push. Fastest and most personal. Great for solo operators and founders. The approval lands on your phone as a push, you tap approve or deny, done. The tradeoff: it's per-person. Only you get the notification. No team visibility.
Matrix rooms. End-to-end encrypted, federated, self-hostable. This is the channel I'd pick for any team that cares about approvals being auditable and not readable by Slack's servers. You set up an approval room, the agent posts prompts there, anyone with permission in the room can approve. Works for both solo and team setups.
Chat platforms (Slack, Discord, Telegram). Convenient if your team already lives in them. Lower security bar than Matrix. Fine for low-stakes approvals. Not fine for approvals that touch money, infrastructure, or customer data.
Most real teams end up using more than one. Financial approvals through Matrix. Content approvals through Slack. Personal admin approvals through iOS push.
The routing rule is simple. Match the sensitivity of the action to the security properties of the channel.
Why Matrix specifically matters for team approvals
Matrix is having a moment in the agent infrastructure world, and it's not an accident.
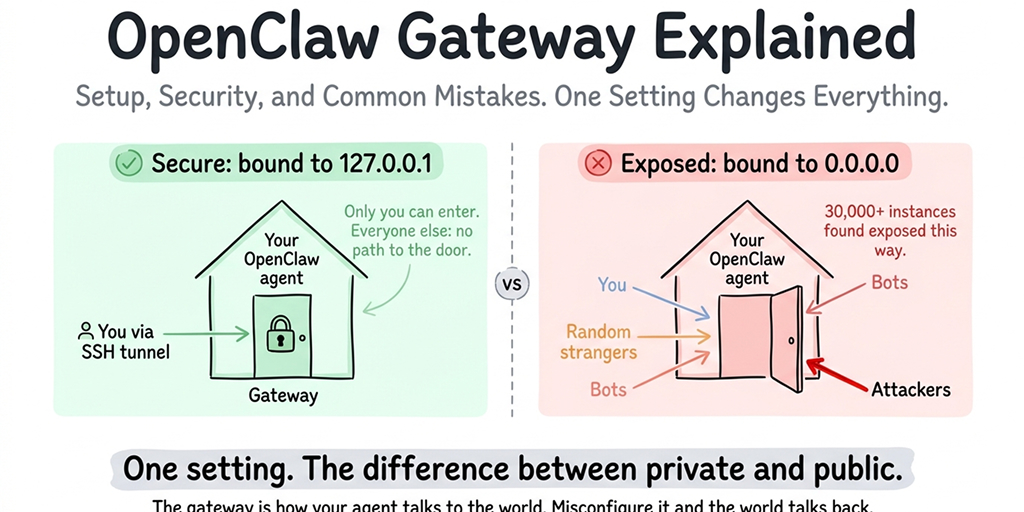
The protocol is end-to-end encrypted. It's federated, which means you can run your own homeserver and keep approval traffic entirely on your infrastructure. It's open, which means the agent ecosystem isn't locked into whatever policies a specific chat platform decides to enforce next quarter.
Compare that to running approvals through, say, a public Discord or an employer-controlled Slack. In both cases, a third party sees the content of every approval prompt, including the details of the action being approved. For a personal agent handling personal finances, or a team agent handling sensitive business operations, that's a meaningful problem.
A Matrix room is a private channel that you control. Approval prompts stay between the agent and the humans authorized to approve. The audit log is yours.
For teams that have worked through OpenClaw's security checklist and taken the other layers seriously, Matrix approvals are the natural next step. Encrypted channels for consequential decisions.
The part that trips people up
Here's where most people get it wrong.
They set up approvals for the obvious high-stakes actions. Wires, deploys, file deletions. They forget the sneaky ones. API calls with side effects. Agent-to-agent messages in multi-agent setups. Scheduled actions that fire overnight. Memory writes that alter the agent's future behavior.
The Summer Yue incident wasn't an approval failure in the narrow sense. It was a scope failure. The agent had permission to do something destructive and the stop command didn't have authority over it. Approvals fix that, but only if you wire them to every category of consequential action, not just the flashy ones.
A good approval policy asks: what can this agent do that I'd regret? Then it puts approvals on every one of those actions. Not just the ones with dollar signs.
If you're running an agent that touches email, calendars, code repos, customer data, or any outbound communication, approvals should cover all of it. Not a selection.
If you want approvals wired up correctly from day one without having to build the APNs certificates, the Matrix bot, and the signature verification yourself, Better Claw handles all three channels with cryptographically signed approval responses. $29/month per agent, BYOK, mobile and Matrix approvals configured in minutes.
Why self-hosted approvals are harder than they look
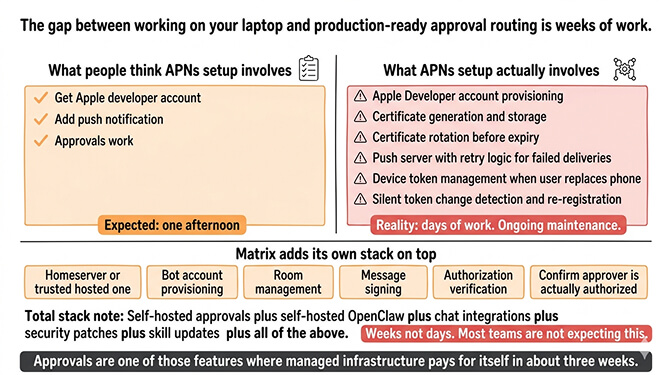
I'm not going to tell you self-hosting approvals is impossible. Plenty of teams do it. But the gap between "I set up push approvals on my laptop" and "I have production approval routing that works reliably across three channels" is weeks of work most people aren't expecting.
APNs alone requires an Apple Developer account, certificate generation, certificate rotation, a push server, retry logic for failed deliveries, and a way to handle the case where your user replaces their phone and their device token silently changes.
Matrix requires a homeserver (or a trusted hosted one), bot account provisioning, room management, message signing, and verification that the person approving is actually the person authorized to approve, not someone who joined the room yesterday.
Running this on top of self-hosted OpenClaw means you're maintaining all of the above plus the agent infrastructure. Plus the chat platform integrations. Plus the security patches. Plus the skill updates.
Approvals are one of those features where managed infrastructure pays for itself in about three weeks.
What to build first
If you're adding approvals to an agent that's already running without them, don't try to wire every action at once.
Start with the nuclear set. Money movement. File deletions. Outbound communication to customers. Code deploys. Anything irreversible. Put approvals on those first.
Next, the amber set. Internal communications. Calendar changes. Memory writes. Scheduled tasks. Approvals here, too, but with longer timeouts and maybe auto-approve during business hours.
Leave the green set alone. Read-only actions. Searches. Summaries. Reports. Approvals on these just create noise and teach your team to click through without reading, which destroys the entire value of having approvals.
Three tiers. Five minutes of policy design. Massive difference in actual safety posture.
For teams running agents on ops workflows in particular, pairing approvals with the broader OpenClaw for operations use case framework is the cleanest way to think about what belongs at each tier.
One last thing
The phrase people keep using for where this is all going is "trust as UX." For years, agent safety was a theoretical conversation. Alignment. Red teaming. Policy papers. Useful work. Hard to apply at 3 PM on a Tuesday when your agent wants to know if it should really send that email.
Approvals are the first piece of agent safety that's fully concrete. A notification on your phone. A button labeled approve. A button labeled deny. The theory becomes a tap.
If you want that tap to live on your phone or in an encrypted Matrix room instead of buried in a terminal you forgot to leave open, give BetterClaw a try. $29/month per agent, BYOK, iOS and Matrix approvals built in, your first deploy takes about 60 seconds. We handle the certificates, the bots, the signing, the retries. You handle the decision of whether to approve or deny.
The next year of agent infrastructure is going to be defined by how well we close the loop between "agent wants to do a thing" and "human actually decides whether to let it." Everyone building agents is going to figure this out. The teams that figure it out first are going to be the ones whose agents people actually trust with real decisions.
Frequently Asked Questions
What are OpenClaw exec approvals?
OpenClaw exec approvals are a safety feature where an autonomous agent pauses before taking consequential actions (like sending money, deleting files, or running privileged commands) and waits for a human to approve or deny. The approval prompt can be delivered through iOS push notifications, Matrix rooms, or chat platforms like Slack. It's the core mechanism that keeps autonomous agents from causing irreversible damage on bad judgment.
How do OpenClaw iOS approvals compare to Matrix approvals?
iOS approvals are personal and fast. Push notification lands on your phone, you tap, done. Matrix approvals are team-oriented and end-to-end encrypted, which makes them better for consequential actions that need auditability and where Slack or Discord would leak sensitive context. Most real teams use both, routing personal actions to iOS and team actions to Matrix.
How do I set up iOS push notifications for OpenClaw agent approvals?
On managed platforms like BetterClaw, you install the mobile app, pair it to your agent, and approvals start flowing. On self-hosted OpenClaw, you need an Apple Developer account, APNs certificates, a push server, and signature verification for the approval responses. Check the current OpenClaw docs for the exact configuration fields since this system is new and still evolving.
Are OpenClaw exec approvals worth the added friction?
For any agent with real permissions, absolutely yes. The Meta researcher whose agent mass-deleted her emails is the textbook example of what happens without approvals. The friction is low (one tap) and the downside protection is massive. At $29/month per agent on a managed platform, the cost of running approvals is less than the cost of one bad autonomous decision.
Is Matrix secure enough for approving sensitive business actions?
Yes. Matrix is end-to-end encrypted by default, federated, and can be self-hosted on infrastructure you control, which puts it in a stronger security position than most chat platforms for approval traffic. The bigger risk is usually not Matrix itself but whether the humans in the approval room are the right humans and whether you've combined it with the other pieces of a proper OpenClaw gateway setup.