Microsoft says don't run it on work machines. Kaspersky found 512 vulnerabilities in the first audit. Belgium issued an emergency advisory. Here's the complete security picture and what to do about it.
On February 19, 2026, Microsoft's security blog published a single sentence that should have stopped everyone cold: "It is not appropriate to run it on a standard personal or corporate machine."
They were talking about OpenClaw. The framework with 230,000+ GitHub stars. 1.27 million weekly npm downloads. Running on 500,000+ instances on the public internet.
Microsoft wasn't alone. Kaspersky published two separate advisories. CrowdStrike issued an enterprise security report. Belgium's Centre for Cybersecurity released an emergency advisory. ARMO, Bitsight, SecurityScorecard, Cisco, Bitdefender, and NVIDIA all published OpenClaw security content. The CVE count passed 138 in under five months.
This is the complete OpenClaw security picture for 2026. Every major vulnerability. Every vendor response. And what each risk means for you.
The vulnerability timeline (it happened fast)
January 25, 2026. The Argus Security Platform ran the first formal audit (filed as GitHub Issue #1796). Result: 512 total vulnerabilities, eight classified as critical. OAuth credentials stored in plaintext JSON files. Authentication disabled by default. WebSocket connections accepted without origin verification.
January 31, 2026. CVE-2026-25253 disclosed. CVSS 8.8. One-click remote code execution through cross-site WebSocket hijacking. Discovered by security researcher Mav Levin (DepthFirst) in approximately 100 minutes of analysis. Patched in v2026.1.29 within 72 hours.
February 2, 2026. Belgium's Centre for Cybersecurity (CCB) published an emergency advisory classifying CVE-2026-25253 as critical, urging organizations to update with "highest priority."
February 5, 2026. China's Ministry of Industry and Information Technology (MIIT) issued a security alert warning that OpenClaw deployments carry "high security risks."
February 10, 2026. Kaspersky published their first advisory. Found that RedLine and Lumma infostealers had already added OpenClaw file paths to their must-steal lists. Configuration files, memory, and chat logs stored API keys, passwords, and credentials in plaintext.
February 19, 2026. Microsoft Security Blog: "It is not appropriate to run it on a standard personal or corporate machine."
March 29, 2026. CVE-2026-32922 disclosed. CVSS 9.9. Critical privilege escalation. A single API call converts a pairing token into full administrative control with RCE capability. ARMO called it "the most severe vulnerability in OpenClaw's history."
April 3, 2026. 1,400+ malicious skills confirmed active on ClawHub. The ClawHavoc campaign included AMOS macOS infostealers bundled into skills disguised as productivity tools (Gmail, Notion, Slack, GitHub integrations).
For the VPS security hardening guide that addresses these specific vulnerabilities, our seven-step guide covers the protections self-hosters need.
138+ CVEs. Two at CVSS 9.9. 512 vulnerabilities in the first audit. Every major security vendor issued warnings. This is not a theoretical risk assessment. It's a documented security crisis.

The three attack surfaces (and which ones are fixable)
Here's what nobody tells you about OpenClaw security. The 138 CVEs fall into three categories, and only one is fully fixable by patching.
Attack surface 1: The gateway (patchable)
CVE-2026-25253 (WebSocket RCE), CVE-2026-32922 (privilege escalation), CVE-2026-24763 and CVE-2026-25157 (command injection). These are code vulnerabilities in the gateway itself. They get patched. You update. The specific vulnerability is resolved.
The problem: New gateway CVEs keep appearing because the architecture was designed for convenience, not security. Authentication disabled by default. Localhost connections implicitly trusted. mDNS broadcasting configuration parameters across the local network. Each convenience creates an attack surface.
Attack surface 2: The skill supply chain (structural)
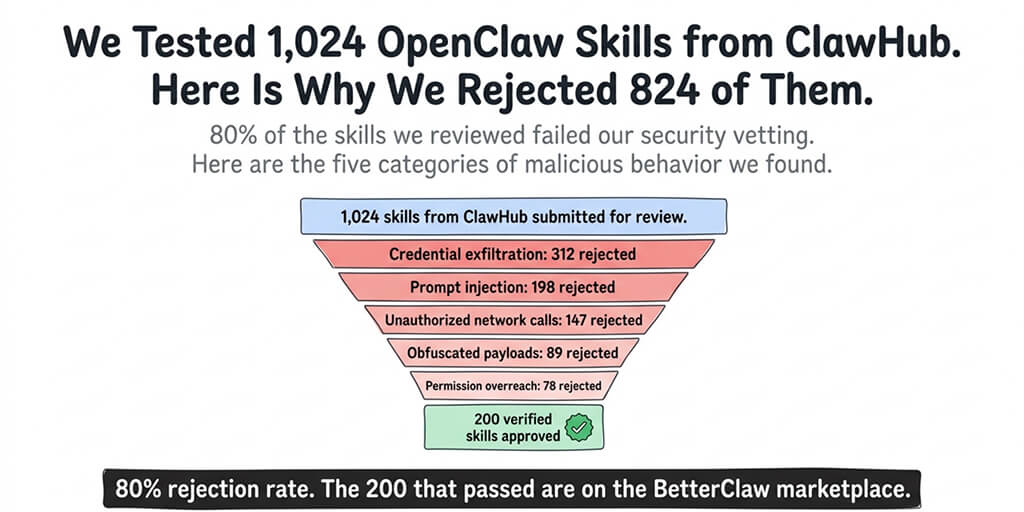
1,400+ malicious skills on ClawHub. Cisco found a skill performing data exfiltration. AMOS infostealers bundled into fake productivity tools. This attack surface can't be patched because it's not a bug. It's a design choice. Anyone can upload a skill. Users install them. The skill runs with the agent's full permissions.
OpenClaw partnered with VirusTotal to scan uploads, and VirusTotal has analyzed 3,000+ skills. But as Kaspersky noted: "it's no silver bullet." Prompt injection payloads and dynamically loaded content evade static analysis.
Attack surface 3: The trust model (fundamental)
This is the one that Microsoft, Kaspersky, and NVIDIA all flagged independently. OpenClaw requires the same system privileges as the user. It accesses files, messaging apps, APIs, and the command line with the user's full permissions. A compromised agent has the same access as a compromised human.
NVIDIA acknowledged this at GTC 2026 by announcing NemoClaw, an enterprise security wrapper. Kaspersky's recommendation: use a dedicated spare computer or VPS, never a primary machine. Microsoft: not appropriate for personal or corporate machines.

What the numbers actually look like
138+ CVEs disclosed across multiple rounds (jgamblin/OpenClawCVEs tracker, 18 pages on OpenCVE).
Two at CVSS 9.9: CVE-2026-22172 and CVE-2026-32922 (admin control without credentials, privilege escalation).
500,000+ instances on the public internet. 135,000+ exposed in 82 countries. 63% without authentication (ARMO, March 2026). SecurityScorecard found 33.8% of exposed infrastructure correlates with known threat actor activity including Kimsuky and APT28 groups.
1,400+ malicious skills on ClawHub. 12% of uploads were malicious in February 2026. Disguised as Gmail, Notion, Slack, and GitHub integrations.
Honeypot scanning began January 26, 2026, the same day OpenClaw hit Hacker News. Attackers mobilized within hours.
1.5 million API tokens exposed through a misconfigured Supabase database belonging to Moltbook (the social network for OpenClaw agents), plus 35,000 email addresses and private messages between agents.

How BetterClaw addresses each attack surface
We're not neutral observers here. We built BetterClaw specifically because these security problems exist. Here's how we address each of the three attack surfaces.
Gateway security: Managed updates applied after testing. Gateway pairing handled by the platform. No user-configurable gateway binding (eliminating the 0.0.0.0 exposure). AES-256 encryption for all stored data. You don't configure security. It's configured for you.
Skill supply chain: Every skill on our verified marketplace is tested by our team before publication. We check for malicious behavior, data access patterns, and security vulnerabilities. This eliminates the 1,400+ malicious skill risk entirely. Not through automated scanning (which Kaspersky called "no silver bullet"). Through human review.
Trust model: Docker-sandboxed execution means skills run in isolated containers, not on the host system. Workspace isolation prevents cross-agent data access. Secrets auto-purge erases credentials from agent memory after 5 minutes, closing the attack vector that RedLine and Lumma infostealers specifically target.
For the complete breakdown of what BetterClaw does differently, our alternative page covers how each security layer works.

What you should do right now (regardless of platform)
If you're running self-hosted OpenClaw:
Update immediately to at least v2026.3.28 (closes CVE-2026-33579 and CVE-2026-32922). Check the jgamblin/OpenClawCVEs tracker for the latest patch status.
Revoke and regenerate all credentials your agent has ever accessed. If OpenClaw was running before the patches, treat the environment as potentially compromised. API keys, OAuth tokens, messaging credentials. All of them.
Audit every installed skill. Skills installed between November 2025 and March 2026 are especially suspect. Uninstall anything you didn't personally verify.
Bind the gateway to loopback. If it's bound to 0.0.0.0, your instance is accessible from the internet.
For the complete VPS security checklist, our checklist covers every hardening step.
The uncomfortable truth
Here's the honest take.
OpenClaw's security problems aren't a series of bugs that got patched. They're a consequence of a design philosophy that prioritized accessibility over security. Authentication disabled by default because it was easier. Localhost trusted implicitly because it was simpler. Anyone can upload skills because it was more open.
That philosophy produced a tool used by hundreds of thousands of people and attacked by nation-state groups within hours of its public launch.
The patches help. The VirusTotal integration helps. But as Kaspersky, Microsoft, NVIDIA, and CrowdStrike all independently concluded: the underlying trust model requires architectural changes, not just patches.
That's what we built BetterClaw to address. Not better patches. Better architecture. Docker-sandboxed execution, verified skills, secrets auto-purge, workspace isolation. The security isn't a layer you configure. It's the foundation the platform is built on.
If your organization is running OpenClaw or evaluating AI agents and security is a concern (it should be), we offer a free AI readiness audit. We identify the highest-impact use cases for your operations, assess the security requirements, share a clear proposal, and if it makes sense, implement it on the BetterClaw platform. No commitment required. The audit is free because the conversation matters more than the sale.
Frequently Asked Questions
How many CVEs does OpenClaw have?
As of April 2026, OpenClaw has 138+ disclosed CVEs tracked across 18 pages on OpenCVE and documented in the jgamblin/OpenClawCVEs GitHub repository. The most severe are CVE-2026-22172 and CVE-2026-32922, both at CVSS 9.9, enabling admin control without credentials and privilege escalation respectively. The first formal audit (January 25, 2026) found 512 total vulnerabilities, eight critical.
What did Microsoft say about OpenClaw security?
On February 19, 2026, Microsoft's Security Blog stated: "It is not appropriate to run it on a standard personal or corporate machine." This recommendation was based on OpenClaw's trust model requiring system-level privileges and the documented vulnerabilities in its gateway and skill supply chain. Microsoft's position aligns with Kaspersky's recommendation to use dedicated hardware or VPS, never primary workstations.
Is OpenClaw safe to use in 2026?
With full hardening (updated to v2026.3.28+, gateway bound to loopback, skills audited, credentials rotated, Docker sandboxing configured), self-hosted OpenClaw can be used cautiously. Without hardening, it is demonstrably unsafe: 500K+ instances exposed, 1,400+ malicious skills, two CVSS 9.9 vulnerabilities. Microsoft, Kaspersky, and CrowdStrike all recommend against deploying on machines with sensitive data. BetterClaw addresses these risks architecturally with sandboxed execution, verified skills, and secrets auto-purge.
What is the ClawHavoc campaign?
ClawHavoc is a supply chain attack campaign targeting OpenClaw users through malicious skills on ClawHub. As of April 2026, 1,400+ malicious skills have been identified, including AMOS macOS infostealers disguised as productivity tools (Gmail, Notion, Slack, GitHub integrations). 12% of ClawHub uploads were malicious in February 2026. OpenClaw partnered with VirusTotal for automated scanning, but security experts note that prompt injection and dynamic loading can evade static analysis.
How does BetterClaw handle OpenClaw's security risks?
BetterClaw addresses all three attack surfaces: gateway vulnerabilities (managed updates, no user-configurable binding), skill supply chain (verified marketplace with human review, not just automated scanning), and the trust model (Docker-sandboxed execution prevents host system access, secrets auto-purge erases credentials after 5 minutes, workspace isolation prevents cross-agent data leakage). Free tier available. $19/month for Pro. Enterprise from $499/month with SAML SSO and audit logs.